Scan Kubernetes Resources with Kubescape
- GeekGuy
- Sep 27, 2022
- 4 min read
Updated: Jun 22, 2023
In this post we are going to see How to Scan Kubernetes resources using Kubescape to secure our Kubernetes cluster.

What is Kubescape?
Kubescape is a K8s open-source tool providing a Kubernetes single pane of glass, including risk analysis, security compliance, RBAC visualizer, and image vulnerability scanning.
How to Scan Kubernetes Cluster Using Kubescape
Security compliance standards are a set of rules, guidelines, and procedures that show developers/DevOps/SRE’s how to protect their clusters and production environments. Kubescape uses security compliance standards and security frameworks such as MITRE ATT&CK and National Security Agency(NSA) to analyze security risks and vulnerabilities found in your cluster. The MITRE ATT&CK framework is used to describe security and model threats; while the NSA has a list of recommendations that guide developers on how they can secure their clusters.
In this section will see, what are possible options available to scan our Kubernetes cluster and resources in Kubescape. To get supported option, you can use following command help command.
# kubescape -h
You can also get detailed information on each command by adding the -h flag.
# kubescape scan -h

The kubescape scan command scans every Kubernetes object available in your cluster and helm charts installed on your cluster. It has the following flags:
--submit: This flag sends the scan results to the Armo management portal.
--enable-host-scan: This flag deploys the ARMO K8s host-sensor DaemonSet that collects valuable and unlimited information from your host machine about your cluster.
--verbose: This flag displays all the resources scanned.
To scan your cluster, use following command,
# kubescape scan --submit --enable-host-scan --format-version v2 --verboseThis scanning command will output all the security analyses of every object in your cluster. As you have provided the submit option it will push the result to armosec portal. So, you can view in detail by login to the portal, as below.

How to Analyze Kubescape Scan Results
The following table contains the risk analysis of the statefulset object. The risk analysis has the following fields:
Threat severity: This field measures how critical the threat is. There are three levels of a threat, which are: High, Medium, and Low.
Control Name: This field states the name of the component or aspect being analyzed.
Docs: This field contains the link that redirects you to a page that contains information about the risk and threat detected during the scan.
Assistant remediation: This field contains changes that can be made to your YAML file or cluster to eliminate the threat.
Vulnerabilities that are classified as Critical/High should be fixed immediately. Use the information from the Docs and Assistance Remediation columns to help you fix the vulnerability detected.
If you use --verbose flag it may show a greater number of lines and your terminal could clear the top ones or your CI build log may look hard to read all. To sort this, you can output the result to PDF format, so you can read it clearly or part of CI/CD process, you can store in some common areas like artifactory repo for security review. You can achieve this by adding --format pdf --output filename.pdf in scan command, as below, this supports for all the scan commands.
# kubescape scan --format pdf --output results.pdf
The scan results.pdf file will be saved in your clusters directory or the directory you are currently using when scanning the cluster.
Kubescape allows you to scan the cluster using your desired security framework such as the NSA framework. All you must do is state the name of the framework as shown below:
# kubescape scan framework nsa
To get pdf report:
# kubescape scan nsa --format pdf --output nsa.pdfYou can also specifically scan containers that have escalated and privilege rights; by adding the control which is “Privileged container”:
# kubescape scan control "Privileged container"
For pdf report.
# kubescape scan control "Privileged container" --format pdf --output container.pdfScan a running Kubernetes cluster with MITRE ATT&CK® framework and submit results to the Kubescape SaaS version
# kubescape scan framework mitre –submit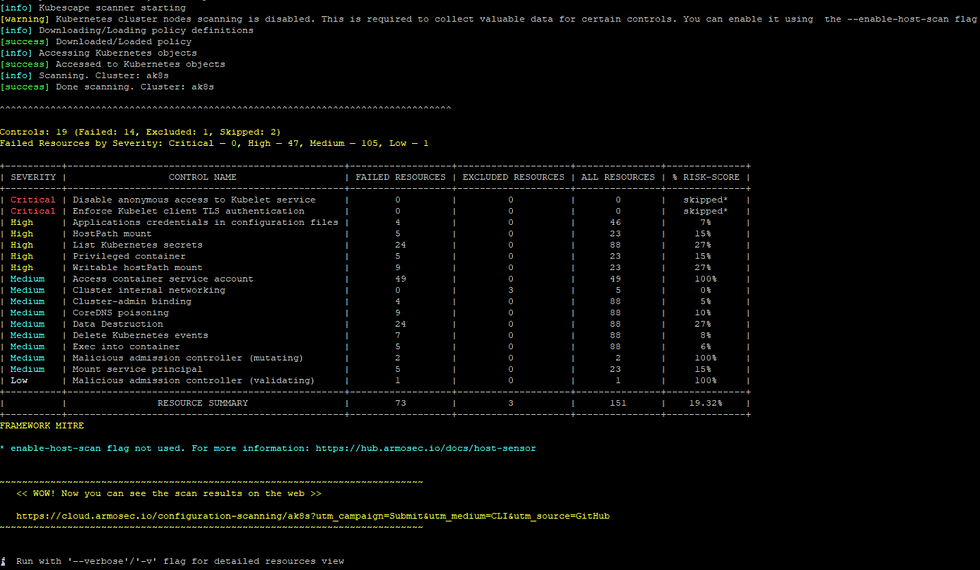
For PDF report,
# kubescape scan framework mitre --format pdf --output mitre.pdfScan specific namespaces
# kubescape scan --include-namespaces staging,productionFor PDF report,
# kubescape scan --include-namespaces staging,production --format pdf --output preprod.pdfScan cluster and exclude some namespaces
# kubescape scan --exclude-namespaces kube-system,kube-publicFor PDF report,
# kubescape scan --exclude-namespaces kube-system,kube-public --format pdf --output teamnamespace.pdfHow to Scan a Specific YAML File
With Kubescape you can scan even single files, for that let me take one file from our previous demonstration, Use the following command to scan the above YAML file:
# kubescape scan sonar-deployment.yaml
For PDF report,
# kubescape scan sonar-deployment.yaml --format pdf --output sonarqube.pdfHow to scan manifests from your Git repository
Kubescape even supports to scan the manifests from the git repository, you can scan the repo by using following command, this will clone the repository and scan the manifests and submit the results.
# kubescape scan https://github.com/foxutech/kubernetes
For PDF report,
# kubescape scan https://github.com/foxutech/kubernetes --format pdf --output kubernetesrepo.pdfOffline/Air-gaped Environment Support
It is possible to run Kubescape offline!
Download all artifacts
Download and save in local directory, if path not specified, will save all in ~/.kubescape
# kubescape download artifacts --output path/to/local/dirCopy the downloaded artifacts to the air-gaped/offline environment, Scan using the downloaded artifacts
# kubescape scan --use-artifacts-from path/to/local/dirDownload a single artifact
You can also download a single artifact and scan with the --use-from flag
Download and save in a file, if the file name is not specified, will save in ~/.kubescape/<framework name>.json
# kubescape download framework nsa --output /path/nsa.jsonCopy the downloaded artifacts to the air-gaped/offline environment, Scan using the downloaded framework
# kubescape scan framework nsa --use-from /path/nsa.jsonConclusion
Threat visibility is a key component in security analysis as it keeps you alert and informs you about all the risks available in your cluster that can be exploited by hackers. Scanning your clusters and YAML files consistently is the best way to start your security audit sessions as they show you all the vulnerabilities that need to be solved immediately. Or you can enable scan part of your CI/CD pipeline, so you can fail even part of pipeline itself, with that you can block the promotion even in lower environment.
When your production environment has passed the Kubescape scan with a 0% risk, your cluster will be compliant with the NSA and MITRE and other frameworks. You can go ahead and apply for different compliance badges. These badges will boost your business’s brand and many clients will trust your services because the security badge is a symbol of high security standards.




Comments